Organizations in today’s fast-paced digital landscape face the constant challenge of ensuring robust health risk efficiency, particularly within virtual private networks (VPNs) and remote operations. Understanding and managing these health risks is critical to safeguarding data security and maintaining seamless operational workflows. In this article, we’ll delve into expert perspectives and practical insights on achieving superior vRops health risk efficiency, incorporating evidence-based strategies, real-world examples, and actionable recommendations.
Key Insights
- Primary insight with practical relevance: Effective vRops health risk management requires a proactive, multi-layered approach that combines advanced monitoring tools with stringent security protocols.
- Technical consideration with clear application: Implementing real-time threat detection systems can drastically reduce potential vulnerabilities, ensuring quicker and more efficient threat response.
- Actionable recommendation: Conduct regular audits and penetration tests to identify and rectify potential weaknesses in your vRops infrastructure.
Proactive Monitoring and Threat Detection
Implementing a proactive approach to monitoring and threat detection is paramount in ensuring vRops health risk efficiency. Traditional reactive methods often come too late, allowing breaches to do significant damage. By leveraging advanced analytics and machine learning, organizations can deploy real-time monitoring systems that not only detect anomalies but also predict potential threats before they materialize. For example, companies like IBM have seen significant improvements in threat detection efficiency by integrating AI-driven security tools into their vRops framework, thereby identifying and neutralizing threats at an earlier stage. These proactive measures allow organizations to maintain a robust defense posture, ensuring minimal downtime and data loss.Multi-layered Security Protocols
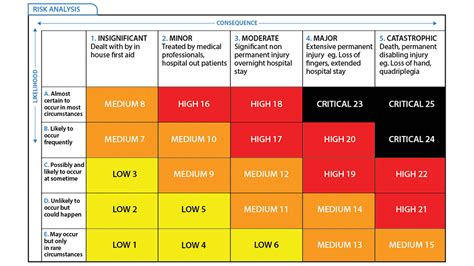
A multi-layered security approach—often referred to as defense in depth—is crucial for maintaining vRops health risk efficiency. This strategy involves deploying multiple security measures across different layers of the network to create a complex barrier against threats. Real-world examples include organizations adopting a combination of firewalls, intrusion detection systems (IDS), and endpoint protection platforms (EPP). A case in point is how financial institutions use this layered approach to thwart sophisticated attacks, such as advanced persistent threats (APTs). By enforcing stringent access controls, data encryption, and network segmentation, organizations can significantly reduce the risk of data breaches and unauthorized access, thereby enhancing overall vRops health risk efficiency.How often should audits and penetration tests be conducted?
Regular audits and penetration tests should be conducted at least quarterly to ensure continuous improvement and adaptation to emerging threats. However, organizations dealing with sensitive data or facing high-risk environments may benefit from more frequent assessments.
What are the main indicators that a vRops system is not efficient in risk management?
Indicators of inadequate vRops health risk efficiency include frequent security breaches, prolonged incident response times, high numbers of failed security tests, and slow patch management processes. Organizations should monitor these metrics to identify areas needing improvement.
Ensuring vRops health risk efficiency is a continuous endeavor that demands a strategic and proactive approach. By integrating advanced monitoring tools, adopting multi-layered security protocols, and performing regular audits, organizations can effectively mitigate potential threats and maintain the integrity and efficiency of their virtual operations.